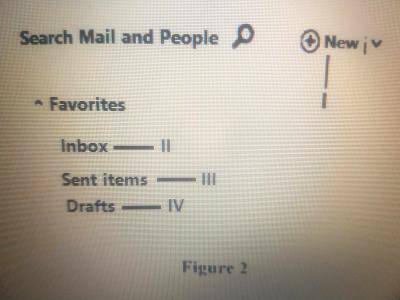
Figure 2 is an email application interface. Use it to answer questions 15 and 16.
To send an e-mail, the user must click on the part labelled
Computer malware is detected by
When performing computer recovery operations after a system crash, the startup disk is used to
The speed of access to files in a random access file compared to other file organization methods is
Which of the following devices is needed by a technician for protection against electrostatic discharge?